Penetration testing tool masquerades as surge protector
In the same way that a hardware keylogger may remain undetected by office workers, Power Pwn – a newly created piece of hardware resembling a power strip or surge protector that is actually a network-snooping device – might pass unnoticed until it’s too late.

Developed by Pwnie Express, a Vermont-based start-up specializing in the creation penetration testing products, the Power Pwn will officially be unveiled this week at Black Hat USA 2012 and Defcon 20.
Preloaded with Debian 6, Metasploit, SET, Fast-Track, w3af, Kismet, Aircrack, SSLstrip, nmap, and a ton of other open source pentesting tools, the device covers the entire spectrum of a full-scale pentesting engagement, from the physical-layer to the application-layer.
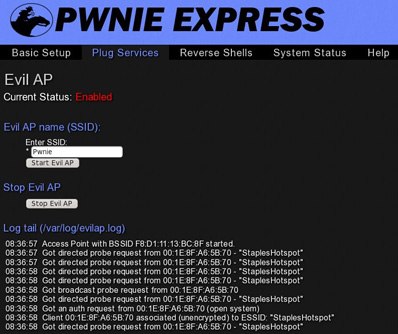
Power Pwn has integrated WiFi and Bluetooth with a range of up to 1000 feet, onboard dual-Ethernet ports, a 16GB internal disk, an external 3G/GSM adapter, provides out-of-band SSH access over 3G/GSM cell networks, the ability for users to text in bash commands via SMS, a web-based administration console, stealth and passive recon modes, and more.
As it stands, the pentester can communicate with the device both via text messages or via the Internet.
A device like this might be created for penetration testers, but will surely also be used by hackers, as even it’s hefty price tag ($1,295) is no longer a barrier for many of them.